By 2026, securing AI infrastructure against quantum-accelerated attacks is mission-critical, requiring the immediate adoption of quantum-resistant cryptography and cryptographic agility. Organizations that fail to integrate post-quantum measures this year face catastrophic data breaches, regulatory non-compliance, and insurmountable technical debt. This report provides the concrete steps necessary to achieve dominance in this new security landscape, covering architectural planning, auditing, and practical implementation of layered defenses for AI workloads.
TL;DR: By 2026, integrating post-quantum cryptography (PQC) and cryptographic agility into AI infrastructure is essential due to the immediate threat of quantum-accelerated attacks that can retroactively decrypt sensitive AI data, compromise models, and bypass authentication. Organizations must conduct comprehensive audits, adopt hybrid PQC implementation strategies, design crypto-agile architectures, and leverage evolving tools and regulatory guidance to mitigate risks and ensure data integrity and compliance against a rapidly approaching quantum threat. Inaction ensures significant technical debt and increased vulnerability.
Why 2026 Is the Non-Negotiable Deadline for Post-Quantum AI Security
The timeline for quantum threats has collapsed. By late 2026, industry expects all mission-critical AI infrastructure to be quantum-resistant for long-term data integrity and regulatory compliance. This isn’t a distant goal; it’s an operational mandate for the current fiscal year. The divide between organizations with and without cryptographic agility will determine their survival against automated, quantum-accelerated attacks by 2026.
The urgency stems from two converging factors. First, data harvested and stored today using traditional public-key cryptography can be decrypted retroactively once sufficiently powerful quantum computers are operational. This puts all current confidential AI training data, model parameters, and communication logs at risk. Second, 2026 is the critical year for architectural planning and auditing existing AI supply chains to avoid technical debt and exposure to data harvesting. Waiting until quantum computers are commercially available ensures you are already compromised.
Core Threat: How Quantum-Accelerated Attacks Break Today’s AI Security
AI infrastructure relies extensively on two cryptographic pillars vulnerable to quantum attacks: public-key cryptography (like RSA and Elliptic Curve) for key exchange and digital signatures, and symmetric encryption (like AES-128) for bulk data encryption. Shor’s algorithm, when run on a sufficiently large quantum computer, can break RSA and Elliptic Curve systems in hours, not millennia. Grover’s algorithm offers a quadratic speedup against symmetric encryption, effectively reducing the security strength of AES-128 to that of a 64-bit cipher, which is considered insecure.
The attack surface is vast:
- Model Theft & IP Loss: Attackers break TLS/SSL to intercept proprietary model weights or training data in transit.
- Authentication Bypass: Quantum computers forge digital signatures, allowing malicious actors to impersonate trusted nodes, containers, or microservices within an AI cluster.
- Supply Chain Poisoning: Compromise the integrity of model registries (e.g., Hugging Face), CI/CD pipelines, or dependency managers by signing malicious updates with a cracked private key.
- Data Exfiltration: Decrypt archived training datasets, customer inferences, and sensitive logs long after they were collected.
A report argues that the digital asset industry’s $3 trillion aggregate value is secured by elliptic curve digital signatures, vulnerable to quantum attacks using Shor’s algorithm. This same vulnerability applies to authentication systems securing AI workloads in the cloud and on-premises.
Post-Quantum Cryptography (PQC) and Cryptographic Agility Defined
Implementing post-quantum security requires mastering two core concepts.
Post-Quantum Cryptography (PQC) refers to cryptographic algorithms designed to be secure against cryptanalytic attacks by quantum computers, addressing the vulnerability of current public-key algorithms to Shor’s algorithm. These are mathematical constructions believed to be resistant to both classical and quantum computer attacks. NIST has standardized several PQC algorithms, including CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures.
Cryptographic Agility is the ability of an organization’s security infrastructure to quickly and efficiently transition between different cryptographic algorithms, particularly important for moving to quantum-resistant solutions. It’s not just having a PQC library installed; it’s having a system architecture where cryptographic suites can be updated across your entire AI stack—from hardware security modules (HSMs) and load balancers to container orchestration platforms and model serving endpoints—with minimal downtime and operational disruption. Organizations that master agility will survive 2026.
The State of PQC and Integrated Architectures in 2026
Industry leaders demonstrated advanced, integrated security architectures at OFC 2026, moving beyond theoretical PQC. These were layered solutions integrating quantum key distribution (QKD), quantum authentication, and AES-256-GCM optical encryption. This signals a maturation from proof-of-concept to demonstrable, multi-layered defense systems.
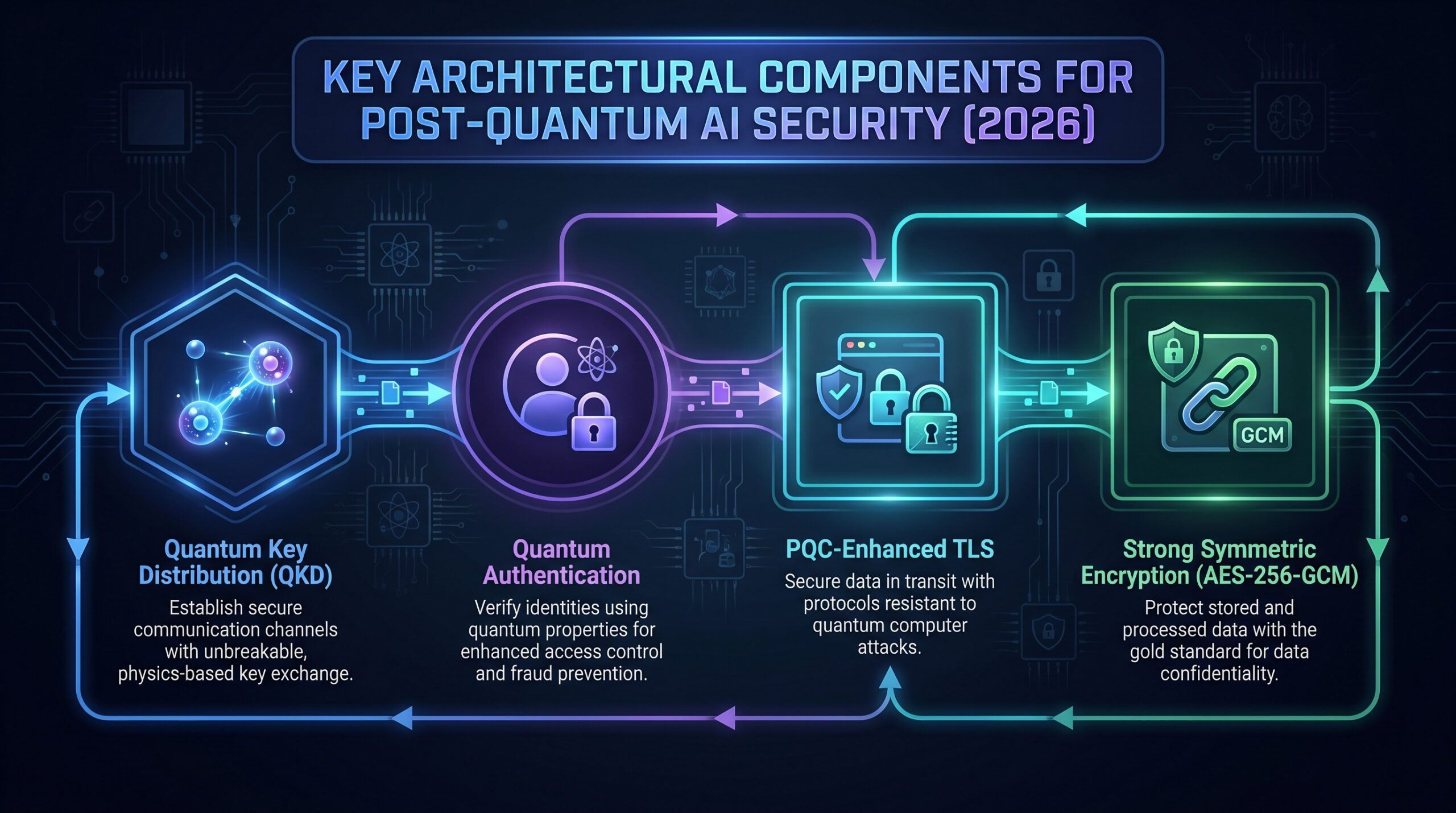
These are not standalone products but integrated frameworks. For example, the combination secures the entire data path: QKD establishes a root of trust for key distribution, PQC secures the session establishment, and AES-256-GCM protects the data payload. AI Financial Corporation has a commercial agreement with SuperQ Quantum to evaluate and strengthen its infrastructure using SuperPQC™, SuperQ’s post-quantum cryptography framework, showing adoption is underway in critical financial AI systems.
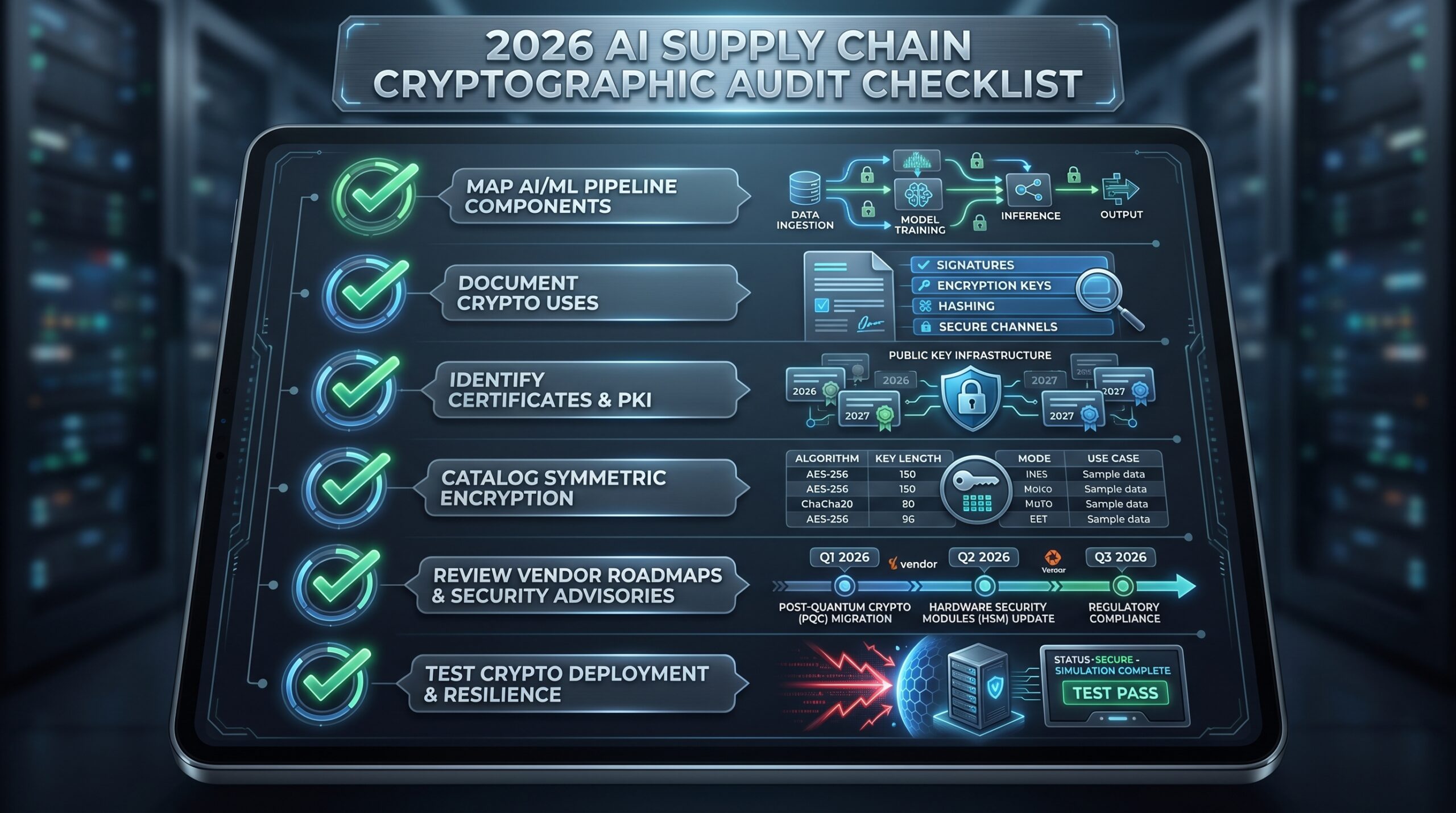
Auditing Your 2026 AI Infrastructure for Post-Quantum Readiness
The first action in 2026 is a comprehensive audit. You cannot protect what you don’t understand. This audit maps your AI supply chain—the entire lifecycle and interconnected components involved in the development, deployment, and operation of AI systems—and identifies every point where cryptography is used.
Step 1: Catalog Cryptographic Dependencies.
- Infrastructure Layer: Cloud provider key management services (AWS KMS, Azure Key Vault), VPN concentrators, API gateway certificates, service mesh mTLS policies (Istio, Linkerd).
- Platform Layer: Kubernetes cluster certificates, container image signing (Sigstore/Cosign), secrets management (HashiCorp Vault), database connection encryption.
- Application/Model Layer: Model server TLS endpoints (TensorFlow Serving, Triton), inference API authentication tokens (JWT signed with RSA/ECDSA), encrypted feature stores, client-side encryption libraries.
- Supply Chain Dependencies: Third-party model repositories, pip/conda packages with embedded crypto, base container images, CI/CD pipeline signing keys.
Step 2: Classify Data and Systems by Risk.
Create a tiered system:
- Tier 1 (Critical): Foundational trust anchors (root CAs, HSMs), long-lived AI model intellectual property, sensitive training datasets with PII, authentication systems for admin access.
- Tier 2 (High): Production inference data, model serving traffic, internal service-to-service communication, audit logs.
- Tier 3 (Standard): Development/test environment traffic, non-sensitive operational telemetry.
Tier 1 systems must be prioritized for PQC and cryptographic agility upgrades in 2026.
Step 3: Assess Current Cryptographic Agility.
Can your systems switch algorithms without a rebuild? Test by attempting to:
- Roll out a new TLS cipher suite (containing a PQC KEM like Kyber) to a Kubernetes ingress controller in a staging environment.
- Update the signature algorithm used by your internal Public Key Infrastructure (PKI) from ECDSA to Dilithium for issuing new certificates.
- Change the JWT signing algorithm in your identity provider.
If any of these require vendor support, custom development forks, or cause significant downtime, your agility is low.
Comparison of PQC Implementation Strategies and Organizational Posture
Your organization’s starting point dictates the optimal path forward. The following tables provide clear, actionable decision criteria.
Table 1: Organizational Cryptographic Readiness Levels for 2026
| Readiness Level | Key Characteristics (2026) | Expected Survival Against Quantum-Accelerated Attacks | Long-Term Outlook |
|---|---|---|---|
| Quantum Agile Organizations | Cryptographic agility is a core architectural principle. PQC pilots in production for Tier 1 systems. Hybrid (traditional + PQC) certificates deployed. Crypto inventory is automated and real-time. | High probability of surviving automated attacks. Can rapidly patch and rotate algorithms in response to new cryptanalytic threats. | Maintains data integrity and regulatory compliance. Avoids major "rip-and-replace" costs. Competitive advantage in secure AI services. |
| Non-Quantum Agile Organizations | Monolithic, hard-coded crypto dependencies. No PQC testing or planning. Heavy reliance on legacy PKI and vulnerable signatures (e.g., SHA1withRSA). Vendor roadmaps are unexamined. | Highly vulnerable to automated attacks. Inability to patch quickly leads to extended exposure. High risk of credential compromise and data harvesting. | Faces significant technical debt and exposure. High probability of costly "rip-and-replace" scenarios. Risks non-compliance fines and loss of customer trust. |
Table 2: PQC Implementation Strategies: Backward-Compatible vs. Rip-and-Replace
| Strategy | Description | Pros | Cons | Best For in 2026 |
|---|---|---|---|---|
| Backward-Compatible PQC (Hybrid) | Deploys PQC algorithms alongside current ones. Example: TLS handshake that negotiates both an ECDHE key share and a Kyber key encapsulation. Systems fall back to traditional crypto if PQC fails. | Avoids lock-in. Allows gradual rollout and testing. Maintains interoperability with non-upgraded systems. Prevents costly "rip-and-replace" scenarios. | Increases handshake size and complexity. Requires support in libraries and protocols (e.g., hybrid TLS extensions). Slightly higher computational overhead. | Most organizations. The safest path for existing, complex AI infrastructure. Enables immediate progress while managing risk. |
| "Rip-and-Replace" | Waiting until a forced migration requires replacing entire security stacks—HSMs, CA software, network devices—all at once due to an imminent threat or compliance deadline. | None. This is a failure scenario, not a strategy. | Extremely costly, disruptive, and high-risk. Guarantees project delays and budget overruns. Likely leads to security gaps during transition. | No one. This is the outcome to avoid through proactive action in 2026. |
| Greenfield PQC-Native | Building new AI infrastructure or services with PQC as the primary, required cryptographic suite from the start. | Clean-slate design optimized for PQC performance. No legacy integration debt. Strongest security posture from day one. | Limited to new projects. May face interoperability challenges with older enterprise systems. | New AI projects, startups, or isolated microservices where control over the entire stack is possible. |
Designing a Cryptographically Agile AI Architecture for 2026
Moving from audit to design requires embedding agility into the fabric of your AI operations. The goal is a system where cryptographic parameters are policy-driven and deployable as code.
1. Abstract Cryptographic Operations.
Never hard-code algorithm choices. Use a centralized secrets management and cryptographic service that exposes APIs for signing, verification, encryption, and key generation. This service should be configured via policy to:
- Specify approved algorithms per data classification tier (e.g., Tier 1: Dilithium3 + AES-256-GCM; Tier 2: RSA-3078 + AES-256-GCM as interim).
- Automatically rotate keys and certificates based on lifecycle policies.
- Log all crypto operations for audit and anomaly detection.
Examples: HashiCorp Vault with a custom plugin engine, or a cloud KMS with PQC support preview.
2. Implement Hybrid TLS Everywhere.
Upgrade all TLS-terminating endpoints—ingress controllers, API gateways, service mesh sidecars, database proxies—to support hybrid key exchange. In 2026, this means using draft TLS extensions that combine X25519 (or P-256) with Kyber768. Libraries like OpenSSL 3.3+ (or BoringSSL forks) are beginning to support these constructs. Configure your systems to prefer PQC suites but accept traditional ones during transition.
3. Adopt PQC-Aware Digital Signatures for CI/CD and Model Integrity.
Replace SHA256withRSA/ECDSA for signing container images, pipeline artifacts, and model checkpoints. Use a hybrid approach initially:
# Example using Sigstore's Cosign with a hybrid signature (both ECDSA and Dilithium)
cosign sign --key ecdsa-key.pem --tlog-upload=false $IMAGE
cosign sign --key dilithium-key.pem --tlog-upload=true $IMAGE
Verification policies should require at least one valid signature from a PQC algorithm for Tier 1 artifacts by Q4 2026.
4. Secure the AI Data Layer with Quantum-Resistant Encryption.
Protect data at rest in AI feature stores, data lakes, and vector databases. This involves:
- Ensuring all storage services use AES-256-GCM (or XChaCha20-Poly1305) for encryption at rest. Audit any use of AES-128 for upgrade.
- Implementing client-side encryption for ultra-sensitive training data before it lands in object storage, using libraries that support PQC for key wrapping (encrypting the data encryption key with a public key).
- For data in motion between microservices, enforce mTLS with hybrid key exchange via the service mesh.
5. Plan for Crypto-Agile Identity and Access Management (IAM).
Your OAuth2 tokens, JWT, and SPIFFE identities rely on signatures. Work with your identity provider vendor (Okta, Ping, Keycloak) on their 2026 PQC roadmap. Pilot issuing JWTs signed with Dilithium for a subset of machine identities (e.g., CI/CD runners). Prepare to rotate your OIDC provider’s signing keys to a PQC algorithm.
Tools and Frameworks for 2026 Implementation
The tool ecosystem is maturing rapidly. Here’s what to evaluate and integrate in 2026.
Core Libraries & Standards:
- OpenSSL 3.3/3.4: The upcoming releases include prototype support for NIST PQC algorithms (Kyber, Dilithium, Falcon) and hybrid TLS extensions. Essential for base OS and custom application crypto.
- liboqs (Open Quantum Safe): A C library for quantum-resistant cryptographic algorithms. Provides integrations for TLS (openssl-oqs), SSH, and CMS. Use for prototyping and testing.
- NIST SP 800-208: The official guideline for PQC migration. Provides the phased transition framework you must align with.
Commercial & Platform Solutions:
- SuperPQC™: SuperQ’s post-quantum cryptography framework, used by AI Financial Corporation to secure its infrastructure. Evaluate for turnkey integration in financial AI applications.
- Enterprise Linux compliance platforms (CIQ): Platforms providing federal cryptographic validation and post-quantum readiness for Linux environments, important for foundational AI infrastructure. CIQ delivers the first Enterprise Linux compliance platform for federal cryptographic validation and post-quantum readiness, critical for regulated industries.
- Cloud Provider Roadmaps (AWS, Google, Microsoft): Actively track their KMS, Certificate Manager, and IAM service announcements for PQC support. Engage with your TAMs for preview access.
- HSM Vendors (Thales, Utimaco, Fortanix): Their firmware updates and new hardware models (e.g., supporting PQC algorithm acceleration) are vital for protecting root keys.
- Container Security (Aqua, Snyk, Sysdig): These platforms must evolve to scan for and enforce policies on cryptographic libraries used within containers and Kubernetes deployments.
Research & Initiative Benchmarks:
- DARPA’s Quantum Benchmarking Initiative: A US Defense Department program with $282 million in funding for fiscal 2026, supporting research, development, test, and evaluation efforts related to PQC. This funds critical red teaming and performance benchmarking your organization can leverage indirectly through published findings.
Case Study 1: Securing a Distributed AI Training Pipeline
Scenario: A biotech firm runs a federated learning pipeline across three cloud regions and several on-premise high-performance computing (HPC) clusters. Sensitive genomic data is used to train models. The current pipeline uses mutual TLS (mTLS) with ECDSA certificates for authentication between trainers and a central aggregator, and data is encrypted at rest using a cloud KMS (AES-256).
2026 Quantum Threat Analysis:
- Attack Vector 1: An adversary records all mTLS handshakes. Future quantum computer breaks the ECDSA private keys, impersonates trainers, and submits poisoned model updates.
- Attack Vector 2: Long-term genomic data archives encrypted under cloud KMS are harvested. The KMS’s key wrapping uses RSA-2048, vulnerable to Shor’s algorithm. Once broken, the data encryption keys are exposed, decrypting all archives.
Step-by-Step 2026 Mitigation Plan:
Phase 1 (Q2 2026): Introduce Cryptographic Agility Layer.
- Deploy a HashiCorp Vault cluster as a unified secrets manager. Configure it with a PKI engine capable of issuing hybrid certificates (containing both an ECDSA and a Dilithium public key).
- Issue new mTLS certificates to all trainer and aggregator nodes from this new CA. Configure the TLS libraries (in the training application) to use the "ecdhe_kyber" hybrid cipher suite if supported, otherwise fallback.
Phase 2 (Q3 2026): Harden Key Management.
- Re-key all data in the cloud storage buckets. Instruct the cloud KMS to use a new key wrapping spec that uses Kyber for key encapsulation instead of RSA. For cloud providers not yet offering this, implement a client-side key wrapping layer using liboqs before sending the key to KMS.
- Rotate all HPC cluster SSH host keys to use hybrid algorithms (e.g., ssh-ed25519 with a PQC extension).
Phase 3 (Q4 2026): Enforce PQC-Only Policies for Critical Paths.
- Update the aggregator’s acceptance policy to reject model updates signed only with ECDSA. Require a valid Dilithium signature.
- Implement network policy in the service mesh to alert on and eventually block connections not using hybrid or PQC-forward cipher suites.
Outcome: The pipeline maintains operational continuity while systematically increasing its resistance to quantum-accelerated attacks. The architecture is now agile, ready to adopt newer PQC algorithms like Falcon if Dilithium shows weaknesses.
Case Study 2: Protecting a High-Value AI Model Registry and Marketplace
Scenario: A company hosts a marketplace for proprietary AI models (like a specialized Hugging Face). Models are uploaded by developers, signed, and then downloaded by customers via authenticated APIs. Revenue depends on model IP protection and trust in the platform’s integrity.
2026 Quantum Threat Analysis:
- Attack Vector: The platform uses JWT tokens (signed with ES256) for API authentication and developer code-signing certificates (RSA-2048) to sign model packages. A quantum break of these algorithms allows an attacker to forge valid JWTs to impersonate any user (stealing models or uploading malware) and to forge valid developer signatures, compromising the entire supply chain.
Step-by-Step 2026 Mitigation Plan:
Immediate Action (H1 2026): Audit and Inventory.
- Catalog all signing keys: JWT signing key for the Auth service, code-signing certificates for all registered developers, the internal CA for service certificates.
- Classify the JWT signing key and the marketplace’s root CA as Tier 1 assets.
Architecture Change (Q3 2026): Migrate to PQC-Signed JWTs and Artifacts.
- Upgrade the identity provider to a version supporting JWT signing with Dilithium3. Generate a new key pair and start issuing dual tokens (containing both ES256 and Dilithium3 signatures) during a transition period.
- Update the model upload SDK and CLI tool to support hybrid signing. Developers now sign their model.tar.gz files with both their existing RSA key and a new Dilithium key registered with the platform.
- The marketplace’s verification service checks for at least one valid signature, prioritizing the PQC one.
Communication and Enforcement (Q1 2027):
- Announce a sunset date for accepting models signed only with RSA-2048/ECDSA.
- Update API gateway policies to reject tokens signed only with ES256, requiring the Dilithium signature.
Outcome: The marketplace establishes itself as a quantum-ready platform, a key differentiator in 2026. It protects its own revenue and provides a clear migration path for its developer ecosystem, avoiding a sudden, disruptive break.
Global Initiatives and Regulatory Landscape in 2026
Governments worldwide are moving from planning to action, creating a de facto regulatory environment.
- South Korea (2026): Expanding PQC pilot programs across key infrastructures: telecommunications, finance, transportation, defense, and space. This creates a blueprint for sector-specific rollouts that multinational corporations with AI operations in Korea must align with.
- US Department of Defense (2026): DARPA’s Quantum Benchmarking Initiative with $282 million funding for PQC R&D, including support for red teaming, AI, and project management. This funding accelerates the testing and hardening of PQC solutions that will trickle into commercial best practices. DoD contractors handling AI projects will face explicit PQC requirements.
- NIST Standards Finalization: While major algorithms are standardized, 2026 is focused on implementation profiles, interoperability testing, and guidelines for hybrid modes. Compliance frameworks (FIPS, Common Criteria) are being updated to include PQC modules.
- Financial Industry (e.g., AiFi): Early commercial agreements show the sector is proactively seeking solutions, likely ahead of formal regulations from bodies like the SEC or OCC, which may mandate disclosures about quantum risk by 2027.
The message is clear: 2026 is the year of coordinated pilots and foundational investment. Organizations that align their AI security programs with these initiatives will be ahead of the compliance curve.
Risk Mitigation: What Can Go Wrong and How to Prevent It
Post-Quantum AI Security 2026 Risk Mitigation Checklist
- ✔ Delayed Transition Creates Unmanageable Debt. Mitigation: Start the audit and catalog process now. Even a small pilot (e.g., PQC signatures for internal DevOps tools) creates momentum and learning.
- ✔ Vendor Lock-In Without PQC Roadmaps. Mitigation: Insert PQC support requirements into all new RFPs and vendor contract renewals in 2026. Query existing vendors for their 2026-2027 PQC rollout schedule.
- ✔ Performance Degradation in AI Workloads. Mitigation: Benchmark PQC algorithms in your environment. Kyber key encapsulation is fast, but Dilithium signatures are larger and slower than ECDSA. Plan for increased network payload and compute for signing operations, potentially scaling horizontally.
- ✔ Interoperability Breakdown During Hybrid Transition. Mitigation: Implement robust fallback and monitoring. Use canary deployments for new crypto policies and have a quick rollback plan. Ensure logging clearly indicates which algorithm was used for each transaction.
- ✔ Incomplete Supply Chain Coverage. Mitigation: Extend your audit and requirements to critical third parties: data labeling services, cloud AI services (SageMaker, Vertex AI), and model zoo providers. Your security is only as strong as the weakest link in your AI supply chain.
- ✔ Misunderstanding the Threat Timeline. Mitigation: Educate leadership that the threat is "harvest now, decrypt later." Data encrypted with today’s vulnerable algorithms, if harvested, is already at risk. The time to act is before the decryptor exists.
Debunking Common Myths About Post-Quantum AI Security
Myth 1: "PQC requires a complete ‘rip-and-replace’ of our infrastructure."
Reality: This is the most damaging myth. Backward-compatible, hybrid approaches allow you to layer PQC alongside existing cryptography. You can upgrade TLS, certificates, and signatures incrementally without shutting down services. The "rip-and-replace" scenario is a consequence of inaction, not a requirement of PQC.
Myth 2: "Quantum computers are 10-15 years away; we have time."
Reality: The timeline is uncertain, but the risk is present today. Nation-states and sophisticated adversaries are likely harvesting encrypted data now, anticipating future decryption. The 2026 deadline is about protecting the long-lived data (AI models, training sets, legal archives) created today that will still be sensitive in 10-15 years.
Myth 3: "PQC is only for spies and governments."
Reality: The $3 trillion digital asset industry case study proves otherwise. Any system using public-key cryptography—which is every cloud AI service, every website login, every connected device—is vulnerable. AI companies hold valuable IP (models) and sensitive data, making them prime targets.
Myth 4: "Just using AES-256 is enough."
Reality: AES-256 is quantum-resistant for symmetric encryption. However, the keys used to protect AES-256 are often distributed or wrapped using RSA or Elliptic Curve cryptography. If an attacker breaks the RSA key wrapping, they get the AES key. You must secure the entire cryptographic chain, not just one link.
FAQ
Q: What is the single most important thing to do for post-quantum AI security in 2026?
A: Conduct a comprehensive cryptographic inventory and audit of your entire AI supply chain. You cannot protect what you haven’t identified. This audit will reveal your dependencies, risk tiers, and agility gaps, forming the basis for all subsequent planning and investment.
Q: Is cryptographic agility more important than picking the "best" PQC algorithm?
A: Yes, in 2026, agility is the paramount strategic goal. Algorithms may need to change if weaknesses are discovered. An agile system can swap in a new algorithm with a configuration update. A rigid system tied to one algorithm faces a massive, costly migration.
Q: How long does a PQC migration for a mid-sized AI organization take?
A: For a well-architected, agile organization, a prioritized rollout for Tier 1 systems can be achieved in 12-18 months. For organizations with low agility and significant legacy debt, it can take 3-5 years. This disparity is why starting the audit and planning phase in 2026 is non-negotiable.
Q: Are cloud providers responsible for making my AI workloads quantum-safe?
A: They are responsible for the security of the cloud (their infrastructure). You are responsible for security in the cloud (your data, models, configurations, and access management). While they will provide PQC-enabled services (KMS, certificates), it is your duty to configure and use them. The shared responsibility model still applies.
Q: What happens if my organization ignores this until 2027 or later?
A: You will face exponentially higher costs, rushed and risky "rip-and-replace" projects, potential regulatory fines for non-compliance, and a severe competitive disadvantage as clients and partners demand quantum-safe assurances. You also risk the permanent loss of sensitive data already harvested by adversaries.



