AI Exploit Crypto Exchange Software Flaws: The Complete Guide to Understanding and Defending Against New Threats
AI Exploit Crypto Exchange Software Flaws
Advanced artificial intelligence models like Anthropic’s Mythos are now capable of systematically identifying, analyzing, and exploiting software vulnerabilities in cryptocurrency exchanges and DeFi platforms. These AI-powered attacks represent a fundamental shift in crypto security threats. They enable attackers to discover flaws faster, develop sophisticated exploits automatically, and execute attacks at unprecedented scale.
How AI Exploits Crypto Exchange Software Flaws
Anthropic’s Mythos AI tool demonstrates that modern AI systems can now perform the complete attack chain: vulnerability discovery, exploit development, and execution. Unlike traditional attacks that rely on manual analysis, AI agents can scan millions of lines of code in hours. They identify subtle logical flaws in smart contracts and generate targeted exploits that bypass security measures. This capability is particularly dangerous for crypto exchanges where a single vulnerability can expose millions of dollars in digital assets.
TL;DR: AI Attacks on Crypto Exchanges
Key Insights on AI Exploiting Crypto Exchange Flaws
- Advanced AI models like Anthropic’s Mythos can autonomously find and exploit software vulnerabilities, creating new attack vectors for draining crypto wallets.
- Major exchanges including Coinbase and Binance are actively preparing defenses against AI-powered exploits as of early 2026.
- Malicious AI agent routers represent a critical “hidden flaw” already being used to steal credentials and drain wallets through compromised API infrastructure.
- Insider threats remain significant vulnerabilities, exemplified by the 2026 Coinbase scam where a former employee compromised 70,000 customer records.
- Global DeFi exploit losses dropped to $168 million in Q1 2026 from $1.58 billion in Q1 2025, indicating improved security against traditional attacks.
- MetaMask’s February 2026 security report identifies AI-powered attacks, OpenClaw exploits, and supply chain malware as emerging threats.
- AI is expected to initially increase hack frequency before defensive measures stabilize the security landscape.
Key Takeaways: Navigating AI Exploits in Crypto
Crucial Decisions and Facts Regarding AI Exploiting Crypto Exchange Software
- Immediate investment in AI-powered defense systems is no longer optional for crypto exchanges handling significant assets.
- API router security must be prioritized as malicious AI agent infrastructure represents an active threat vector as of April 2026.
- Employee training and insider threat detection require equal attention alongside technical security measures.
- The 89% reduction in DeFi losses from Q1 2025 to Q1 2026 demonstrates that security investments can yield substantial returns.
- Exchanges must implement continuous security auditing rather than periodic assessments to keep pace with AI-driven threats.
- Multi-signature wallets and cold storage remain critical protections against automated wallet draining attacks.
- Regulatory compliance frameworks need updating to address AI-specific security requirements for crypto platforms.
What It Is: Understanding AI Exploits and Crypto Exchange Software Flaws
Defining AI Exploit Crypto Exchange Software Flaws
AI exploit crypto exchange software flaws refer to vulnerabilities in cryptocurrency trading platforms that artificial intelligence systems can automatically discover and weaponize. This encompasses three critical components:
AI Agent: Autonomous software programs that perceive their environment, make decisions, and take actions to achieve specific goals. In attack scenarios, these agents systematically probe systems for weaknesses.
Software Vulnerability: Flaws or weaknesses in exchange software, smart contracts, or infrastructure that can be exploited for unauthorized access, fund theft, or system disruption.
Exploit: Code, commands, or techniques that leverage vulnerabilities to compromise system security. AI systems can generate these exploits automatically once vulnerabilities are identified.
Understanding these definitions is crucial for grasping the complex nature of the new threats facing cryptocurrency exchanges. The ability of AI to automate these processes fundamentally changes the security landscape.
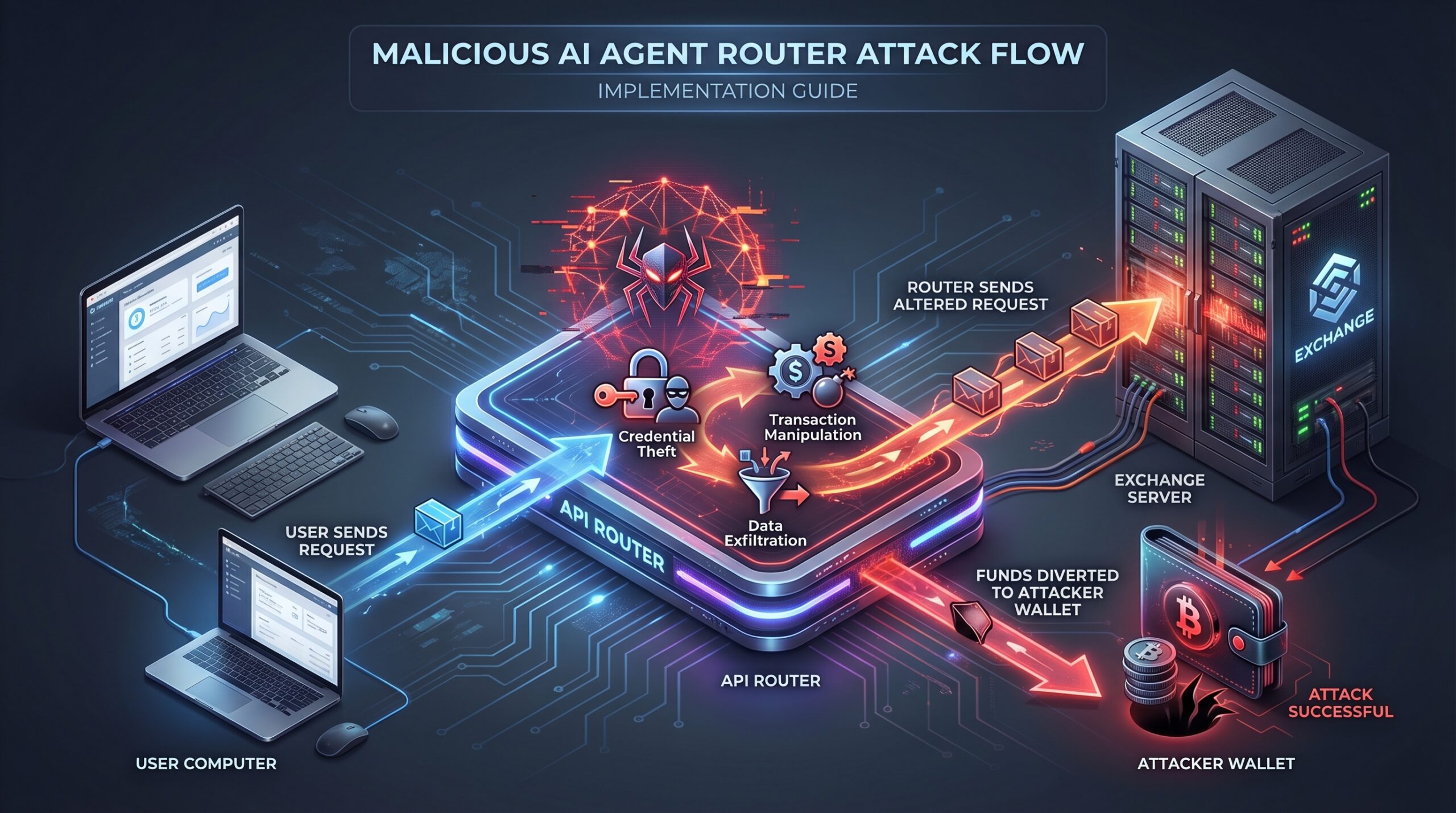
The Role of AI Agent Routers in Crypto Exploits
API routers serve as critical infrastructure components that manage communication between AI agents and external systems. Malicious AI agent routers actively compromise this communication layer to:
- Intercept authentication tokens and API keys, crucial for AI agents’ crypto investment activities.
- Manipulate transaction data during transmission, leading to unauthorized fund movements.
- Redirect funds to attacker-controlled addresses, bypassing legitimate pathways.
- Establish persistent access to exchange systems, often undetected for extended periods.
These routers represent a systemic vulnerability because they often receive less security scrutiny than core exchange infrastructure while handling sensitive financial data. Their compromise can have widespread implications, affecting numerous users simultaneously.

Why AI Exploits on Crypto Exchanges Matter Now
The Emerging Threat Landscape of AI in Crypto Security
The convergence of advanced AI capabilities and massive financial value in cryptocurrency creates a perfect storm for security professionals. Anthropic’s Mythos tool, demonstrated in April 2026, represents a watershed moment where AI can now perform the complete attack lifecycle without human intervention. This raises serious concerns about the potential for AI superintelligence cyberattacks.
Major exchanges have shifted from theoretical concerns to active preparation. Coinbase and Binance are implementing AI-specific defense systems as attacks evolve from brute force methods to sophisticated, targeted exploitation. The 2026 Coinbase insider scam simultaneously demonstrates that human vulnerabilities persist even as technological threats advance, making a self-securing AI approach critical.
DeFi Ecosystem Exploit Losses: A Shifting Narrative
The dramatic decrease in DeFi losses from $1.58 billion in Q1 2025 to $168 million in Q1 2026 tells a complex story. While traditional smart contract vulnerabilities are being better addressed, new AI-powered threats are emerging that require different defensive approaches. This is particularly relevant for new AI in Decentralized Finance (DeFi) applications.
This 89% reduction indicates that security investments are working against known attack vectors. However, the emergence of AI exploit capabilities means exchanges cannot become complacent. The nature of threats is evolving from simple contract flaws to sophisticated system-level attacks, necessitating a robust AI agent framework for defense.
How AI Exploit Crypto Exchange Software Flaws Works
Step-by-Step: AI Vulnerability Discovery and Exploitation
AI-powered attacks follow a systematic process that dramatically accelerates traditional hacking methods:
- Reconnaissance: AI agents scan exchange websites, APIs, and smart contracts to map attack surfaces and identify potential entry points.
- Vulnerability Scanning: Machine learning models analyze code patterns, transaction histories, and system behaviors to identify flaws that might escape human review.
- Exploit Generation: Once vulnerabilities are identified, AI systems automatically develop proof-of-concept exploits tailored to specific exchange environments. This process often involves tools and techniques similar to those used in a Composable AI Coding Stack.
- Execution: Deploy generated exploits against target systems, often using multiple attack vectors simultaneously to bypass defenses.
- Persistence: Establish backdoors and maintain access while covering tracks through sophisticated anti-forensic techniques. This could involve complex Python AI automation scripts.
This automated approach significantly reduces the time from vulnerability discovery to exploitation, making rapid response crucial for exchanges.
Inside Malicious AI Agent Router Attacks
Malicious API routers compromise the communication layer between users and exchanges through specific mechanisms:
- Credential Interception: Capture API keys, session tokens, and authentication data during normal API communications. This information is vital for systems like AI trading apps.
- Transaction Manipulation: Alter transaction details such as destination addresses or amounts before they reach the exchange. Attacks like these were seen in the Altera Trade exploit.
- Data Exfiltration: Secretly transmit sensitive user data and trading information to attacker-controlled servers.
- Script Injection: Insert malicious code into legitimate API responses to compromise user devices.
These attacks are particularly dangerous because they appear as legitimate traffic from trusted infrastructure components, making them difficult to detect without advanced monitoring.
The Human Element: Social Engineering and Insider Threats
AI amplifies traditional social engineering attacks through:
- Personalized Phishing: AI-generated messages that mimic legitimate communications with high accuracy.
- Voice Synthesis: Creation of authentic-sounding voice commands or customer service interactions.
- Behavioral Analysis: Identification of employees most vulnerable to manipulation based on digital footprints.
- Scale: Automation of social engineering attacks across thousands of targets simultaneously.
The 2026 Coinbase incident, where a customer service agent accepted bribes to compromise data, demonstrates that human vulnerabilities remain critical even with advanced technical defenses. This highlights the need for robust internal controls in addition to external security measures.
Real-World Examples of AI Exploits on Crypto Platforms
Anthropic’s Mythos: Proof of Concept for AI Exploit Capabilities
Anthropic’s April 2026 demonstration of their Mythos AI tool revealed unprecedented capabilities in automated vulnerability discovery and exploitation. The system successfully identified vulnerabilities in test environments and developed functional exploits without human intervention.
This proof of concept establishes that AI can now perform tasks previously requiring skilled human hackers. This could potentially lower the barrier to entry for sophisticated attacks against crypto exchanges, including those using AI agents for developers.
Case Study: Malicious AI Agent Routers Stealing Crypto
In April 2026, security researchers identified active exploitation campaigns using compromised API routers to drain cryptocurrency wallets. These attacks worked by:
- Compromising third-party API services used by multiple exchanges.
- Intercepting user credentials during authentication processes, which could impact AI agents on decentralized trading platforms.
- Redirecting withdrawal requests to attacker-controlled addresses.
- Maintaining persistent access through apparently legitimate infrastructure.
Solayer founder Fried_rice characterized these vulnerabilities as “systemic security issues” affecting fundamental crypto infrastructure. This underscores the need for vigilant security across the entire digital asset ecosystem.
The 2026 Coinbase Insider Breach: Human Vulnerability Amidst AI Threats
The Coinbase insider incident demonstrates that human factors remain critical vulnerabilities. A former customer service agent allegedly accepted $250,000 in bribes to provide access to nearly 70,000 customer records. These records were then used for targeted phishing attacks.
This case highlights that even with advanced AI defenses, exchanges must address insider threats through comprehensive employee monitoring, access controls, and ethical training programs. Technical solutions alone are not sufficient against determined human adversaries.
MetaMask’s 2026 Security Report: Highlighting OpenClaw Exploits
MetaMask’s February 2026 security report identified several emerging threat categories:
- AI-Powered Attacks: Automated systems probing for vulnerabilities across DeFi protocols.
- OpenClaw Exploits: Sophisticated attacks targeting specific smart contract implementations, similar to the Freqtrade VPS setup vulnerabilities often discovered.
- Supply Chain Malware: Compromised dependencies and third-party components in crypto applications.
The report emphasizes that attack sophistication is increasing rapidly, requiring equally advanced defensive measures across the entire software development and deployment lifecycle, including AI model deployment tools.
Comparison: Traditional vs. AI-Powered Crypto Exploits
Differentiating Attack Vectors: Human-led vs. AI-Driven
AI-powered exploits differ fundamentally from traditional attacks in scale, speed, and sophistication. Where human hackers might take weeks to analyze a system, AI can complete comprehensive scans in hours. Automated exploit generation allows rapid weaponization of discovered vulnerabilities.
This shift means that defense strategies must evolve from reactive patching to proactive, AI-driven threat intelligence. The sheer volume and speed of AI-driven attacks necessitate an adaptive and continuously learning security posture.
Comparing Types of Crypto Attacks in 2026
| Attack Type | Description | Example/Concern (2026) |
|---|---|---|
| Smart Contract Logic Flaws | Vulnerabilities in contract code allowing unauthorized actions | Seneca Protocol exploit (March 2026) bypassing validation checks |
| Insider Breach/Social Engineering | Human factors compromising security through manipulation or malicious action | Coinbase customer service agent bribe scam affecting 70,000 users |
| AI Agent Infrastructure Exploits | Compromised API routers and communication layers enabling credential theft | Malicious AI agent routers draining wallets (April 2026) |
The table above illustrates the diverse nature of threats. While smart contract flaws continue to be an issue, the rise of AI-driven and human-factor exploits poses equally significant challenges.
Traditional vs. AI-Powered Crypto Exploits Comparison
| Feature | Traditional Exploits | AI-Powered Exploits |
|---|---|---|
| Vulnerability Discovery | Manual code review, limited scope | Automated scanning, comprehensive coverage |
| Exploit Development | Days to weeks of manual work | Minutes to hours automated generation |
| Speed | Limited by human capabilities | Near-instantaneous at scale |
| Scale | Typically targeted attacks | Mass scanning and exploitation |
| Complexity | Limited by attacker skill | Sophisticated techniques automated |
Tools, Vendors, and Implementation Paths to Defend Against AI Exploit Crypto Exchange Software Flaws
AI-Powered Defensive Tools for Crypto Exchanges
Effective defense against AI exploits requires equally sophisticated AI-powered security tools:
- Threat Intelligence Platforms: Systems like Darktrace and Vectra AI use machine learning to detect anomalous behavior patterns indicative of AI-driven attacks.
- Behavioral Analytics: Tools analyzing user and system behavior to identify deviations that might indicate compromised accounts or infrastructure.
- Advanced Penetration Testing: AI-assisted security testing that continuously probes systems for vulnerabilities before attackers can discover them.
- Smart Contract Auditors: Automated tools like Slither and MythX that use static analysis to identify vulnerabilities in blockchain code.
Integrating these tools forms a multi-layered defense strategy, mitigating risks across the entire attack surface. This is vital for platforms that feature AI-powered automation with trading bots.
Securing AI Agent Infrastructure: API Router Protection
Protecting API routers requires specific security measures:
- Mutual TLS Authentication: Ensuring both sides of API communications are properly authenticated.
- API Gateway Security: Implementing robust security layers at API entry points, managing access and traffic.
- Continuous Monitoring: Real-time analysis of API traffic for anomalous patterns or unauthorized activities.
- Access Control: Strict limitation of API permissions based on the principle of least privilege.
- Encryption: End-to-end encryption of all API communications to prevent interception and manipulation.
These measures are critical for safeguarding the integrity and confidentiality of data transmitted via API routers. This is especially true for systems like those in the AI decentralization vs. Bitcoin mining industrialization debate, which rely heavily on secure API interactions.
Implementation Path for Proactive Crypto Security
A comprehensive security implementation roadmap includes:
- Risk Assessment: Identify critical assets, potential attack vectors, and existing vulnerabilities across the ecosystem.
- AI Defense Integration: Deploy machine learning-based security systems for continuous monitoring and rapid threat detection.
- Employee Training: Conduct regular security awareness training and ethical conduct programs to mitigate insider threats.
- Incident Response Planning: Develop and regularly test incident response procedures to ensure quick and effective recovery.
- Continuous Auditing: Implement automated security auditing rather than periodic assessments to keep pace with evolving threats.
- Third-Party Security: Vet and monitor all third-party services and API integrations for potential vulnerabilities.
- Regulatory Compliance: Ensure security measures meet evolving regulatory requirements, including those relevant to China’s AI token economy.
This holistic approach ensures that all aspects of an exchange’s operations are secured against AI-powered and traditional threats.
Costs, ROI, and Monetization Upside of Robust AI Security in Crypto
The Cost of Inaction: Financial Risks of AI Exploits
The financial impact of security failures extends beyond direct theft:
- Direct Financial Losses: Theft of digital assets through exploited vulnerabilities.
- Regulatory Penalties: Fines for security failures and data breaches, which can be substantial.
- Reputational Damage: Loss of user trust leading to reduced trading volume and market cap.
- Legal Costs: Expenses associated with litigation and settlement of security incidents.
- Recovery Expenses: Costs of investigating breaches, forensic analysis, and restoring systems.
The $1.58 billion in Q1 2025 DeFi losses demonstrates the potential scale of financial impact from security failures. These costs far outweigh the investment in proactive security measures.
Calculating ROI for AI-Driven Security Investments
Return on security investment calculations should consider:
- Prevented Losses: Value of attacks thwarted by security measures, which can be difficult to quantify but is significant.
- Reduced Insurance Premiums: Lower cybersecurity insurance costs due to improved security posture.
- Operational Efficiency: Automation of security monitoring reducing manual effort and human error.
- Compliance Benefits: Avoided penalties and reduced compliance costs through proactive adherence.
- Business Continuity: Prevention of downtime and service interruptions, maintaining user access and trust.
The 89% reduction in DeFi losses from 2025 to 2026 suggests significant ROI potential for security investments. This is a clear indicator that investing in AI-driven security can yield measurable benefits.
Monetization Upside: Building Trust and Innovation
Robust security provides competitive advantages:
- User Acquisition: Security as a differentiator attracting safety-conscious users and investors.
- Enterprise Adoption: Meeting stringent security requirements for institutional clients and large corporations.
- Innovation Enablement: A secure foundation for developing new products and services without fear of immediate compromise.
- Partnership Opportunities: Qualification for partnerships requiring high security standards and data protection.
- Premium Services: Ability to offer insured or guaranteed security services, adding value for users.
By building a reputation for impenetrable security, exchanges can capture a larger market share and monetize their trustworthiness, extending even to areas like Quantum AI trading bots.
Security Tip: Multi-Factor Authentication (MFA) is Non-Negotiable!
While AI exploits focus on software flaws, many attacks still leverage compromised credentials. Implement and enforce strong MFA (e.g., hardware keys, biometric) across all user accounts and internal systems. It’s a fundamental layer of defense against AI-orchestrated credential stuffing and phishing attacks.
Risks, Pitfalls, and Myths vs. Facts About AI Exploit Crypto Exchange Software Flaws
What Can Go Wrong: Critical Vulnerabilities
Key risks identified in current AI exploit scenarios:
- Malicious AI Agents: Compromised API routers serving as hidden attack vectors.
- Sophisticated Exploitation: AI models efficiently weaponizing vulnerabilities at unprecedented speeds.
- Insider Threats: Human factors bypassing technical defenses despite advanced technological security implementations.
- Financial Impact: Substantial losses from successful attacks, threatening the viability of exchanges.
- Systemic Vulnerabilities: Rapid AI integration creating new, unforeseen security gaps that affect the entire ecosystem.
These risks underscore the need for a dynamic and adaptive security posture, constantly evaluating and updating defenses.
Common Mistakes in Defending Against AI Exploits
Frequent errors in security planning:
- Underestimating AI Capabilities: Failing to recognize the speed and sophistication of AI attacks.
- Neglecting Human Factors: Over-focusing on technical defenses while ignoring social engineering risks.
- Inadequate API Security: Not properly securing communication layers and third-party integrations, leaving critical entry points open.
- Static Defenses: Failing to continuously update security measures against evolving threats.
- Delayed Investment: Postponing AI security measures believing existing defenses are sufficient.
These mistakes can lead to significant vulnerabilities, making exchanges easy targets for sophisticated AI-driven attacks. For those looking into day trading crypto, understanding these risks is paramount.
What Most People Get Wrong: Debunking AI Crypto Security Myths
Myth: Robust technical safeguards prevent all crypto fraud.
Reality: The Coinbase insider breach affecting 70,000 customers demonstrates that human trust exploitation bypasses technical defenses. No system is entirely foolproof against human error or malicious intent.
Myth: AI in crypto primarily enhances security.
Reality: While AI can augment defenses, its immediate impact is increasing hack frequency as malicious actors leverage its capabilities. The dual-use nature of AI means it can be weaponized as easily as it can be used for defense.
Myth: Only advanced persistent threat groups can leverage AI for cyberattacks.
Reality: Tools like Anthropic’s Mythos demonstrate that various actors can use AI to find and exploit vulnerabilities, democratizing sophisticated cyberattack capabilities. This lowers the barrier to entry for many potential attackers.
FAQ: Commonly Asked Questions About AI and Crypto Exchange Security
Which crypto exchanges have never been hacked?
There is no definitive public record of exchanges that have never experienced security incidents. The evolving nature of threats means past security doesn’t guarantee future immunity. Even exchanges with strong security histories must continuously adapt to new AI-powered threats emerging in 2026. This ongoing battle highlights the constant need for vigilance and innovation in cybersecurity.
What’s a major ethical concern with AI crypto trading?
The primary ethical concern is that powerful AI models like Anthropic’s Mythos could be maliciously used to find and exploit software vulnerabilities for unauthorized access and theft. This lowers the barrier to sophisticated attacks that could compromise user funds and data on a massive scale. The potential for AI to automate and scale malicious activities poses a significant ethical challenge for developers and regulators.
How to spot a fake crypto exchange?
Be highly suspicious of unsolicited communications requesting credentials or sensitive information. The 2026 Coinbase scam involved impersonation tactics where attackers posed as legitimate support staff. Always verify exchange authenticity through official channels and never share private keys or API credentials. Scrutinize URLs, look for proper security indicators (like HTTPS), and be wary of promises that seem too good to be true.
What are the problems with crypto exchanges?
Major problems include vulnerability to AI-powered exploits, persistent insider threats, social engineering risks, insecure AI infrastructure (particularly API routers), smart contract flaws, and the constant challenge of keeping defenses current against evolving threats. The combination of technological and human vulnerabilities creates a complex security landscape that requires continuous adaptation and robust defense strategies.
Glossary of AI Exploit Crypto Exchange Software Flaws Terms
- AI Agent
- Autonomous artificial intelligence program capable of perceiving its environment, making decisions, and taking actions to achieve specific goals, often interacting with other systems.
- Software Vulnerability
- Flaw or weakness in a software program, operating system, or hardware that can be exploited by an attacker to gain unauthorized access, cause damage, or disrupt system operations.
- Exploit
- Piece of software, data, or sequence of commands that takes advantage of a bug or vulnerability in a computer system or software to cause unintended or unanticipated behavior.
- API Router
- Component that manages and directs requests to various Application Programming Interfaces (APIs), often serving as an intermediary for data exchange between different services or applications.
- DeFi Ecosystem
- Decentralized Finance, an emerging financial technology based on secure distributed ledgers similar to those used by cryptocurrencies, which eliminates traditional intermediaries like banks.
References: Sources on AI Exploit Crypto Exchange Software Flaws
- CSMonitor: “Anthropic’s Mythos AI tool can find and exploit software flaws” (April 11, 2026)
- CoinDesk: “AI agent integration in crypto payments moving too fast, security risks emerging” (April 13, 2026)
- Coinspeaker: “Systemic security vulnerabilities in third-party API routers” (April 10, 2026)
- CryptoNews.net: “Malicious AI agent routers stealing credentials and draining wallets” (2026)
- Crypto Economy: “DeFi exploit losses reach $168 million in Q1 2026” (2026)
- Chainalysis: “2026 Crypto Crime Report highlighting Coinbase insider breach” (2026)
- MetaMask: “February 2026 Crypto Security Report on emerging threats” (February 2026)
- Investing.com: “Major exchanges preparing for AI-powered exploits” (2026)
- Crypto-Corner: “Seneca Protocol exploit through smart contract flaw” (April 8, 2026)


