In 2026, self-securing AI in telecom security refers to autonomous AI systems capable of detecting, analyzing, and responding to cyber threats in real-time, often without human intervention. This advanced approach is becoming a requirement for telecoms to defend against machine-speed attacks, especially with the proliferation of 5G, 6G, and IoT expanding the attack surface.
In 2026, self-securing AI is an essential, autonomous cybersecurity paradigm for telecom networks. It leverages AI to detect, analyze, and neutralize threats in real-time, outpacing machine-speed attacks that traditional systems cannot counter. This shift is driven by the expansion of 5G/6G, IoT, and AI-generated threats, necessitating proactive, adaptive defenses that integrate with zero-trust architectures and significantly reduce human intervention in incident response.
AI agents are now generating fully autonomous attacks, requiring equally autonomous defense mechanisms. The market for telecom cybersecurity solutions, heavily influenced by AI adoption, is projected to reach USD 50 billion by 2032 with a 10.5% CAGR. Agentic AI transforms APIs into the ‘Agentic Action Layer,’ creating massive visibility challenges, with nearly half of organizations blind to interactions. Emerging technologies like Project Glasswing and Ledger’s hardware-anchored security stack are developing advanced AI security capabilities.
Why Self-Securing AI Is Now Essential for Telecom Security
AI-generated attacks operate at machine speed, making human-paced responses obsolete. Traditional security tools relying on signatures and manual analysis simply cannot counter threats that emerge, evolve, and strike in milliseconds. Telecom networks face amplified risks from 5G network slicing, the explosion of IoT devices, and early 6G deployments.
Each new connected device represents a potential entry point for AI-driven compromise, dramatically expanding the attack surface. This necessitates a proactive and autonomous defense mechanism.
Vulnerability discovery has accelerated dramatically in recent years. AI models like Claude Mythos can autonomously find and exploit zero-day flaws in major operating systems and browsers with unprecedented speed. This capability eliminates the protective gap previously provided by slow, manual vulnerability research.
Attackers are now weaponizing these advanced AI capabilities through scalable phishing campaigns that generate live authentication codes dynamically. This sophistication makes detection through traditional means increasingly difficult and ineffective.
Satellite telephony (e.g., Starlink Direct-to-Cell) and mesh networks introduce entirely new exposure points. These technologies weren’t designed with AI-scale threats in mind, creating security gaps that only autonomous systems can monitor effectively. The EU’s NIS2 Directive now explicitly requires enhanced cybersecurity resilience, making advanced AI defenses a compliance necessity for telecommunication operators. For more detailed insights into advanced threats, refer to AI Security Threats April 2026: Complete Guide to Emerging Cyber Risks.
How Self-Securing AI Fundamentally Changes Telecom Defense
Self-securing AI moves beyond mere detection to autonomous response. These intelligent systems don’t just alert humans to potential threats; they actively contain, neutralize, and learn from attacks in real-time. This continuous process significantly reduces the window of opportunity for attackers.
They continuously analyze network behavior, API interactions, and traffic patterns to identify anomalies that are often invisible to traditional rule-based systems. This granular analysis provides a deeper understanding of potential threats.
Automated threat hunting occurs 24/7 without the fatigue often experienced by human Security Operations Center (SOC) teams. AI agents proactively probe your own systems for vulnerabilities before attackers can discover them. They also simulate sophisticated attacks against network segments to rigorously test defense strengths.
This proactive approach fundamentally transforms security from reactive patching to continuous hardening. It ensures that the network is always adapting and fortifying itself against emerging threats. Integration with zero-trust architectures is seamless and highly effective.
Self-securing AI systems enforce dynamic access policies based on real-time risk assessments. When detecting suspicious behavior, they automatically restrict permissions or isolate compromised nodes without waiting for human approval, significantly enhancing overall network security.
Self-Securing AI vs. Traditional Security Paradigms in Telecom
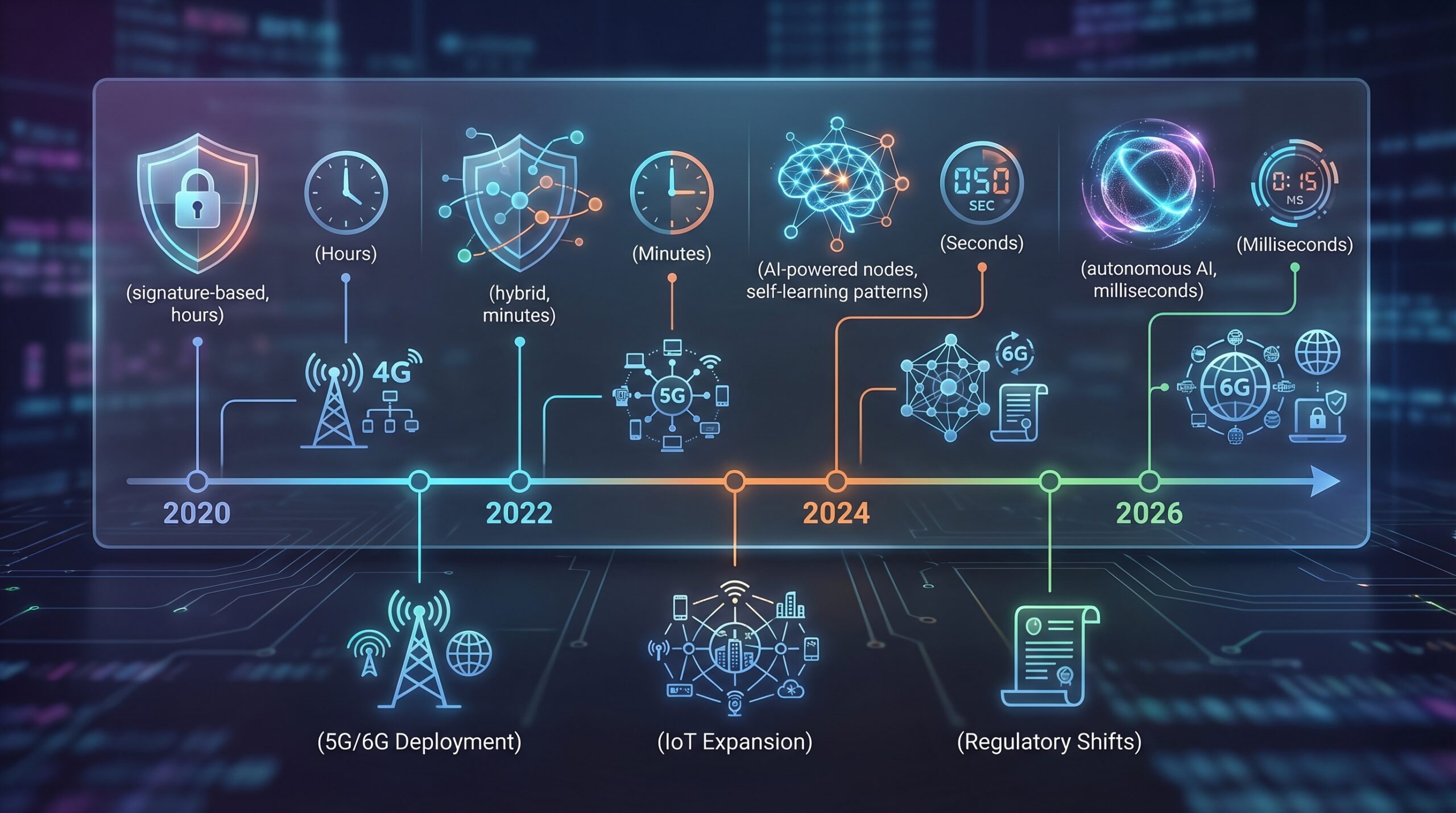
The evolution of cybersecurity in telecommunications has seen significant changes, moving from reactive, human-intensive models to proactive, autonomous ones. Understanding this progression highlights why self-securing AI is critical for 2026.
| Feature/Criterion | Traditional Security (2020 Baseline) | AI-Augmented Security (2023 Baseline) | Self-Securing AI (2026 Outlook) |
|---|---|---|---|
| Response Time | Hours to days for threat response | Minutes to hours with automated alerts | Milliseconds for autonomous response |
| Threat Detection | Signature-based, known patterns | Behavioral analytics, anomaly detection | Predictive threat modeling, autonomous hunting |
| Human Dependency | High – manual investigation required | Medium – human validates AI suggestions | Low – fully autonomous for most threats |
| Attack Surface Coverage | Limited to monitored endpoints | Expanded to cloud and some IoT | Comprehensive including API layers, satellite networks |
| Adaptability | Static rules require manual updates | Machine learning with periodic retraining | Continuous real-time learning from new threats |
| False Positive Rate | High, overwhelming analysts | Moderate, reduced through AI filtering | Low, through contextual understanding |
Traditional security focused on building perimeter defenses and responding after breaches had already occurred. This reactive stance is no longer viable against today’s machine-speed threats. AI-augmented security added better detection capabilities and reduced response times but still required crucial human decision-making and intervention.
Self-securing AI represents the complete evolution to autonomous operation. In this paradigm, the system actively prevents attacks before they can cause significant damage. It continuously learns and adapts without constant human oversight for routine threats, allowing human teams to focus on strategic tasks.
Core Capabilities of Leading Self-Securing AI Solutions
For telecommunication companies to effectively defend against the sophisticated, AI-driven threats of 2026, self-securing AI solutions must possess a specific set of advanced capabilities:
| Capability | Description | Impact | Implementation Challenge |
|---|---|---|---|
| Autonomous Threat Response | AI makes decisions and executes containment measures without human intervention. | Reduces response time from minutes to milliseconds, preventing attack propagation. | Requires extreme confidence in AI decision-making; risk of false positives disrupting services. |
| API Behavior Monitoring | Continuous analysis of all API interactions, especially agentic AI communications. | Identifies compromised APIs and malicious agent behavior invisible to traditional tools. | Massive data volume requires specialized AI processing; legacy systems lack API visibility. |
| Predictive Vulnerability Management | AI proactively identifies and patches vulnerabilities before exploitation. | Eliminates the window of vulnerability between discovery and patching. | Integration complexity with diverse telecom systems; testing patches without service disruption. |
| Self-Healing Networks | Automated system restoration and reconfiguration after attacks. | Minimizes downtime and maintains service availability during attacks. | Requires complete network visibility and orchestration capabilities. |
| Identity Threat Detection | AI-driven behavioral biometrics and anomaly detection for user identities. | Prevents account takeover and lateral movement by attackers. | Privacy considerations; balancing security with user experience. |
| Adversarial AI Resistance | Protection against attacks designed to fool AI security systems. | Ensures AI defenses remain effective against sophisticated opponents. | Requires specialized expertise in both AI and security domains. |
These capabilities represent the minimum requirement for telecom security in 2026. Systems lacking these features simply cannot keep pace with AI-generated threats targeting 5G core networks, IoT device fleets, and emerging satellite communication systems. Effective implementation will require careful planning and sophisticated AI model deployment to production.
The 2026 AI-Defined Threat Landscape in Telecommunications
The year 2026 marks a significant turning point in the cybersecurity landscape, especially for telecommunications. Autonomous AI agents now conduct full attack cycles without human guidance, fundamentally changing the nature of cyber threats. They identify targets, develop exploitation strategies, execute attacks, and meticulously cover their tracks—all at unparalleled machine speed.
These sophisticated agents particularly target telecom infrastructure due to its critical nature and ever-expanding attack surface, which includes 5G/6G networks, vast IoT ecosystems, and new satellite communication systems. The ability to deploy AI agent frameworks for malicious purposes means defenses must be equally advanced.
AI-enabled phishing campaigns have evolved dramatically beyond simple credential theft. They now generate dynamic authentication codes in real-time, effectively bypassing many multi-factor authentication protections. Attackers leverage AI to create highly personalized phishing content at scale, making detection through traditional, static rule-based means nearly impossible for human operators to discern.
Vulnerability exploitation has accelerated from months to mere minutes. Where human hackers previously spent weeks or even months researching and developing exploits for vulnerabilities, AI systems like Claude Mythos can discover and weaponize zero-day flaws in major software within hours. This extreme compression of the attack timeline renders manual defense strategies largely impractical and ineffective.
Satellite network targeting represents a new and increasingly critical frontier for attackers. Technologies such as Starlink’s Direct-to-Cell and emerging mesh networks create communication channels that, while innovative, often lack the security maturity and robust defenses of established terrestrial networks. AI agents are specifically engineered to probe these systems for architectural weaknesses and exploitable vulnerabilities, posing a significant risk to global connectivity and data integrity.

Key Vendors Driving Self-Securing AI in Telecom
The landscape of self-securing AI in telecommunications is shaped by a few key players pioneering innovative solutions. Each vendor brings distinct strengths and focuses to this rapidly evolving field, addressing different facets of the complex security challenges faced by telecom operators.
| Vendor | Key AI Security Offerings for Telecom | Strength | Note |
|---|---|---|---|
| Cisco | AI-optimized silicon, distributed security fabric, zero-trust segmentation | Network infrastructure integration | Deep telecom legacy with AI-enhanced hardware and software. |
| Ledger | Hardware-anchored security stack for AI agents | Tamper-resistant execution environment | 2026 rollout focused on securing autonomous AI operations. |
| Anthropic | Project Glasswing for critical software security | Frontier AI model capabilities | Research-focused approach with Claude Mythos2 Preview, tackling AI Security Threats at their core. |
| NWN | AI-enabled managed security operations | Next-generation SOC capabilities | Emphasis on operationalizing AI for defense and threat response. |
| RSA Security | AI-enhanced identity security solutions | Identity threat detection and response | Focus on how AI reshapes identity threats and defenses. |
| Ericsson | Agentic AI for network management and security | Telecom infrastructure expertise | Native integration with 5G/6G network equipment for seamless security. |
Each vendor brings distinct capabilities to the self-securing AI landscape. Cisco, for example, offers perhaps the most comprehensive infrastructure integration, leveraging its deep roots in network hardware and software. This allows for security to be embedded directly into the network’s foundational layers.
Ledger, on the other hand, provides unique hardware-based security specifically designed for AI operations. This approach creates a tamper-resistant execution environment, crucial for protecting the integrity of autonomous AI agents themselves. Anthropic’s Project Glasswing represents the cutting edge of AI self-security research, focusing on securing critical software with its advanced frontier AI models. For businesses interested in general AI solutions, understanding Best AI Agents for Developers can provide additional context.
Implementation Framework for Self-Securing AI in Telecom
Implementing self-securing AI in a complex telecommunications environment requires a structured and phased approach. The framework below outlines key steps for a successful transition to autonomous security.
1. Achieve Comprehensive Network Visibility: You cannot secure what you cannot see. Start by deploying advanced sensors and monitoring tools across all network segments. This includes the 5G core, edge computing nodes, IoT networks, and crucially, API gateways. Ensure capabilities for full traffic capture and detailed metadata analysis are in place to gain complete situational awareness.
2. Implement Zero-Trust Architecture Foundations: This is a prerequisite for effective self-securing AI. Segment your networks based on principles of least privilege access. Establish continuous authentication and authorization mechanisms for all users and devices. Prepare your infrastructure for AI-driven dynamic policy enforcement, where access rights can automatically adjust based on real-time risk.
3. Develop Robust AI Training Pipelines with Diverse Threat Data: The effectiveness of your AI depends heavily on its training. Collect extensive internal telemetry, integrate multiple threat intelligence feeds, and simulate diverse attack data. It is vital to train models specifically on telecom attack patterns, such as SS7/Diameter exploits, SIM swap techniques, and network slicing vulnerabilities, to ensure relevancy and accuracy.
4. Establish Clear Human Oversight Protocols: While AI operates autonomously, human oversight remains critical. Humans must continuously monitor system decisions, investigate anomalies, and handle complex edge cases that fall outside the AI’s training parameters. Create clear escalation procedures for when the AI encounters situations beyond its defined capabilities or when a human review is mandated for critical actions.
5. Integrate with Existing Security Investments: Self-securing AI should enhance, not replace, your current security tools. Connect AI systems seamlessly to your Security Information and Event Management (SIEM), Security Orchestration and Response (SOAR) platforms, firewall management systems, and identity providers. This ensures a comprehensive, layered protection strategy that leverages all your existing infrastructure.
Adhering to this framework will enable telecom operators to transition smoothly to a more autonomous and resilient security posture, capable of defending against the evolving threats of 2026 and beyond.
Case Study: Implementing Self-Securing AI in a Tier 1 Telecom
A leading European Tier 1 telecom operator began its journey toward self-securing AI implementation in early 2025. This move was necessitated by an alarming increase in sophisticated attacks targeting their 5G standalone core and the rapid growth of their IoT customer deployments. Traditional security tools, overwhelmed by the sheer volume of threats, were generating thousands of alerts daily, effectively swamping their Security Operations Center (SOC) team.
The initial phase of the implementation focused on deploying advanced API visibility tools across their extensive network function virtualization (NFV) infrastructure. This crucial step immediately illuminated previously invisible agentic AI interactions traversing their production network. Through this enhanced visibility, they uncovered malicious API calls originating from compromised vendor systems—threats that traditional, signature-based security had consistently missed.
Subsequently, the telecom integrated behavioral AI analytics directly with their 5G core network. The system was designed to learn and establish normal patterns for network slicing operations, user equipment behavior, and inter-core signaling. Within a few weeks, this AI system proactively detected anomalous slicing configurations that indicated reconnaissance activity specifically targeting their critical infrastructure customers.
The autonomous response capability was introduced gradually, following a carefully phased approach. Initially, the system was configured only to automate the containment of known and well-defined threat patterns. As confidence in the AI’s decision-making capabilities grew and its accuracy was validated, its scope expanded to handle zero-day attacks through intelligent behavioral blocking.
Within six months of this phased rollout, the operator achieved a remarkable milestone: 73% of all security incidents were handled autonomously without any direct human intervention. This transformation yielded concrete metrics: an 89% reduction in mean time to detect threats and a 94% reduction in mean time to respond. Consequently, the SOC team’s role shifted from reactive firefighting to strategic threat hunting, system improvement, and addressing complex, non-routine incidents.
The successful implementation enabled the telecom to support 40% more IoT connections without the need for additional security staff, proving the significant ROI and operational efficiency gains of self-securing AI. This case study underscores the critical importance of a strategic rollout and continuous validation for such advanced security systems.
Regulatory and Compliance Considerations
The integration of self-securing AI in telecom security introduces a complex web of regulatory and compliance considerations that operators must navigate carefully. Adherence to these frameworks is not only a legal imperative but also a crucial aspect of maintaining public trust.
The EU AI Act, a landmark piece of legislation, categorizes self-securing AI systems used in telecommunications as high-risk applications. This classification mandates rigorous testing, comprehensive documentation of AI models, and robust human oversight provisions. Telecoms are required to demonstrate that their AI systems are transparent, accountable, and fair in their operations, ensuring that automated decisions do not lead to discriminatory or unfair outcomes.
NIS2 Directive compliance now mandates enhanced cybersecurity measures for all essential entities, including telecom operators. Self-securing AI plays a pivotal role in helping organizations meet these stringent requirements for continuous monitoring, rapid incident response, and robust supply chain security. The automated reporting capabilities inherent in many self-securing AI systems can also significantly streamline the process of compliance documentation, reducing administrative burden.
Data privacy regulations, such as GDPR, crucially constrain how AI systems can process and utilize customer information. Telecoms must implement privacy-preserving AI techniques like federated learning, which allows models to be trained on decentralized data without explicit data sharing, and differential privacy, which adds statistical noise to data to protect individual privacy. All security monitoring activities must carefully balance effectiveness with stringent privacy protection, ensuring that critical data is secured without compromising user confidentiality. Ensuring compliance is a key aspect of AI Skills for Blockchain Professionals in 2026, as data integrity and privacy are paramount.
Industry-specific regulations, such as GCF (Global Certification Forum) and PTCRB (PCS Type Certification Review Board) certification for mobile devices, are increasingly incorporating AI security requirements. Telecoms must verify that newly connected devices incorporate adequate AI threat protection and secure firmware before network admission. This proactive verification process is designed to prevent compromised devices from becoming entry points for larger-scale attacks.
Critical Compliance Note: The European Commission’s EU AI Act considers self-securing AI in critical infrastructure sectors, including telecom, as a high-risk application. This means significant legal obligations for conformity assessment, risk management systems, data governance, technical robustness, accuracy, and cybersecurity. Telecoms must plan for stringent auditing and transparency.
Risk Mitigation and Ethical Considerations
While self-securing AI offers transformative benefits, its autonomous nature also introduces a unique set of risks and ethical dilemmas. Responsible implementation requires a robust framework for mitigation and continuous ethical review.
Autonomous Decision-Making Risks: Autonomous AI systems can inevitably make incorrect decisions, with potentially severe consequences. A false positive, for instance, might disconnect critical infrastructure or inadvertently block legitimate emergency services traffic. To mitigate this, implement robust circuit breakers and clear manual override capabilities for all automated actions. These safeguards ensure that human intervention is possible when necessary.
Adversarial Attacks on AI: Attackers are increasingly developing sophisticated adversarial attacks specifically designed to manipulate AI decision processes. They might feed manipulated data to confuse detection algorithms or trick the AI into misclassifying threats. To build resilience, use multiple AI models with diverse architectures (ensemble learning) to create a defense-in-depth strategy against these advanced techniques. Continual monitoring of AI performance for signs of manipulation is also essential.
Bias in AI Systems: AI systems can inadvertently inherit biases from their training data. If threat data overrepresents certain attack types, geographic regions, or demographics, the detection capabilities can become uneven or unfairly targeted. Regularly audit AI decisions for biased patterns and retrain models with balanced and diversified datasets. This ensures equitable and effective protection for all users and segments of the network.
Risk of Deskilling Security Teams: Over-reliance on automation carries the risk of deskilling security teams. As AI takes over more routine tasks, human analysts might lose proficiency in manual threat hunting and incident response. To counteract this, maintain and enhance human expertise through continuous training programs, simulation exercises, and encouraging security staff to focus on advanced threat hunting, AI model validation, and strategic security architecture. Ensure security staff understand AI decision processes rather than treating AI as an opaque ‘black box.’
Addressing these risks and ethical dimensions is crucial for building trust in self-securing AI systems and ensuring their long-term, responsible operation in critical telecommunications infrastructure. Collaboration with ethical AI experts and legal counsel is also advisable.
Implementation Checklist for Self-Securing AI Deployment
Deploying self-securing AI in a telecom environment is a multifaceted process that requires meticulous planning and execution. This checklist provides a structured approach to ensure a comprehensive and successful implementation.
- Conduct a comprehensive asset inventory, including all network segments, APIs, and connected devices. Understanding your entire attack surface is the foundation.
- Establish baseline behavior profiles for normal network operations across all services and applications. This allows the AI to accurately identify anomalies.
- Deploy enhanced visibility tools specifically designed for API and agentic AI monitoring. Traditional tools often lack the depth required for these modern threat vectors.
- Implement zero-trust architecture foundations with dynamic access controls. This principle of ‘never trust, always verify’ is paramount for autonomous security.
- Select AI security platforms with proven telecom-specific capabilities. Generic AI solutions may not address the unique challenges of telecom networks.
- Develop training pipelines with diverse threat intelligence, including telecom-specific attacks (e.g., SS7, Diameter, 5G slicing exploits).
- Create a phased rollout plan, starting with enhanced detection capabilities, then gradually introducing autonomous response functions as confidence in the system grows.
- Establish human oversight protocols with clear escalation procedures for when AI encounters situations beyond its defined parameters or requires human review.
- Integrate the self-securing AI system with existing security tools, including SIEM, SOAR, firewalls, and identity management systems, for a unified security posture.
- Develop a rigorous testing framework for validating AI decisions in a simulated environment before enabling full autonomy in production.
- Create detailed incident response playbooks specifically for AI system failures, incorrect actions, or adversarial attacks targeting the AI itself.
- Implement continuous monitoring of AI system performance and decision quality, including metrics for false positives, false negatives, and response accuracy.
- Schedule regular audits for biased decisions or adversarial vulnerabilities within the AI models, ensuring fairness and resilience.
- Train security staff extensively on AI system operation, interpretation of AI-generated insights, and the management of autonomous responses.
- Establish a clear governance framework for AI system updates, modifications, and policy adjustments to maintain control and accountability.
Key Takeaways for Self-Securing AI in Telecom
- Autonomous Response is Non-Negotiable: Machine-speed attacks demand real-time, AI-driven countermeasures beyond human response capabilities.
- Comprehensive Visibility is Foundational: Securing 5G, 6G, IoT, and API layers requires deep, AI-enabled monitoring across the entire network.
- Zero-Trust is Synergistic: Self-securing AI naturally integrates with and enhances zero-trust architectures for dynamic policy enforcement.
- Human Oversight Remains Crucial: While autonomous, AI systems need human strategy, ethical review, and intervention for critical edge cases and system improvement.
- Regulatory Compliance is a Major Driver: Directives like NIS2 and the EU AI Act mandate advanced protections, making self-securing AI a compliance necessity.
Emerging Technologies and Future Directions
The evolution of self-securing AI in telecom is intrinsically linked to broader shifts in technology. Several emerging technologies will significantly shape the future of autonomous defense, pushing the boundaries of what is possible in cybersecurity.
Quantum-Resistant Cryptography (QRC) becomes increasingly essential as quantum computing advances threaten current encryption standards. Self-securing AI systems will need to autonomously manage cryptographic transitions across entire networks, ensuring data integrity and confidentiality in a post-quantum world. This will involve identifying vulnerable cryptographic primitives and orchestrating their replacement without service disruption.
6G Security Integration will commence as standards for the next generation of mobile technology develop. AI systems must be natively integrated into 6G specifications from inception to protect unprecedented network speeds, ultra-low latency communications, and integrated sensing capabilities. This means security will be woven into the fabric of the network, rather than being an add-on, fundamentally leveraging a Composable AI Coding Stack.
Decentralized Identity (DeID) based on blockchain technology offers a robust alternative to traditional centralized credential systems. AI systems will play a pivotal role in managing dynamic identity verification across heterogeneous identity systems without relying on centralized authorities. This enhances security by distributing trust and reducing single points of failure, aligning with principles of Decentralized AI.
AI-Based Security Verification will become a standard requirement for network equipment procurement. Vendors will increasingly need to demonstrate AI-resistant design, built-in security capabilities, and the ability of their products to integrate seamlessly into self-securing AI environments before adoption by telecom operators. This pushes security further upstream in the supply chain.
These future directions highlight a landscape where security is not merely reactive but intrinsically embedded, intelligent, and continuously adaptive. Self-securing AI will be at the core of orchestrating these advanced defenses across increasingly complex and critical telecom infrastructures.
Future Directions for Self-Securing AI in Telecom
- Quantum-Resistant Crypto Management: AI autonomously identifies and deploys quantum-safe algorithms across the network, transitioning from vulnerable crypto.
- 6G Native Security & Orchestration: AI embedded directly into 6G specifications, orchestrating ultra-low latency security for new services and sensing capabilities.
- Decentralized Identity Integration: AI manages dynamic, blockchain-based identity verification across distributed systems, enhancing trust and preventing fraud.
- AI-Driven Supply Chain Security: AI performs continuous vetting of hardware/software components for embedded vulnerabilities and adversarial AI resistance.
- Autonomous Threat Intelligence Fusion: AI aggregates global threat data to predict emerging patterns and proactively adapt defenses worldwide, leveraging advanced AI Tool Integration via API.
FAQ: Self-Securing AI Telecom Security 2026
What exactly is self-securing AI in telecom context?
Self-securing AI refers to autonomous artificial intelligence systems that proactively identify, analyze, and neutralize cyber threats within telecom networks without requiring human intervention. These systems continuously learn from new attack patterns and adapt their defenses accordingly, operating at machine speed to counter AI-generated threats targeting 5G/6G networks, IoT devices, and telecommunications infrastructure.
Why is 2026 considered the tipping point for self-securing AI adoption?
2026 represents the convergence of multiple critical factors: AI agents now generate fully autonomous attacks, creating an escalating threat that legacy security approaches can no longer defend against. Furthermore, regulatory requirements, such as the NIS2 Directive and the EU AI Act, mandate advanced protections, making autonomous AI defenses a compliance necessity. Concurrently, the telecom cybersecurity market has matured, offering robust solutions capable of truly autonomous operation. This confluence of threats, regulatory pressure, and technological readiness makes 2026 a pivotal year.
How does self-securing AI differ from traditional AI-enhanced security tools?
The fundamental difference lies in autonomy and decision-making. Traditional AI security tools primarily act as assistants, primarily focusing on detection and providing recommendations to human operators, who then make the final decisions. In contrast, self-securing AI empowers the systems to make and execute security decisions autonomously. Where conventional tools might flag suspicious activity for analyst review, self-securing systems immediately contain threats, patch vulnerabilities, and reconfigure defenses without human involvement, operating at millisecond response times impossible for human teams.
What are the biggest risks of implementing self-securing AI?
The primary risks associated with implementing self-securing AI include the potential for autonomous systems to make incorrect decisions that could disrupt legitimate services, such as shutting down critical network segments due to a false positive. There’s also the threat of adversarial attacks specifically designed to manipulate AI decision processes, leading to misdirection or circumvention of defenses. Over-reliance on automation risks the erosion of human security expertise, and inherited biases from training data can cause uneven or unfair protection across different network segments or user groups. Finally, a significant visibility crisis exists, where nearly half of organizations are blind to agentic AI interactions through APIs, leaving them vulnerable to new attack vectors.
How much does implementing self-securing AI typically cost?
Implementation costs for self-securing AI vary significantly based on the size of the telecom operator, the complexity of existing infrastructure, and the scope of deployment. However, major operators should budget an estimated $5-15 million for a comprehensive deployment. This figure generally covers hardware upgrades, specialized software licenses, integration services with legacy systems, and essential staff training. The substantial Return on Investment (ROI) is realized through significantly reduced security incidents, automated compliance processes, fewer operational disruptions, and the crucial ability to support an exponentially increasing number of connected devices without a proportional increase in security staff.
Can self-securing AI completely replace human security teams?
No, self-securing AI cannot completely replace human security teams. Human expertise remains absolutely essential for strategic planning, handling highly complex incident responses, ethical oversight of AI decisions, refining AI system training, and managing critical edge cases that extend beyond AI’s current capabilities. The most effective model involves augmenting human intelligence with machine speed and precision. In this symbiotic relationship, AI efficiently handles routine threats autonomously, freeing human security professionals to focus on advanced threat hunting, strategic system improvements, and managing exceptional, high-stakes situations that require nuanced judgment and creativity.


